So what is it?nms ag4040 quad t1/e1
Posted via [H] Mobile Device
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
So what is it?nms ag4040 quad t1/e1
i tried trixbox, debian, and suse,
no luck, the card doesn't have drivers for NIX look like that
looks like it works on solaris
fwiw most multi-port network cards (and with scsi) I've seen are for sun systems.

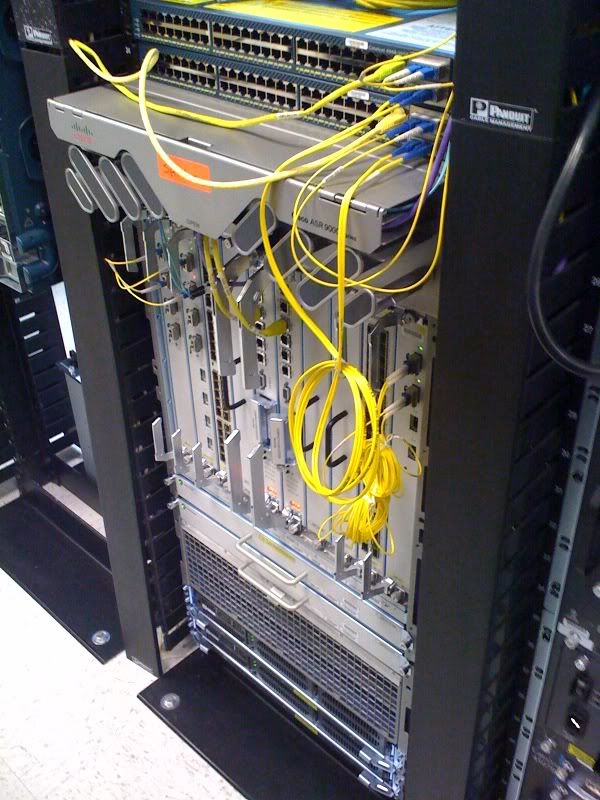
finally posting a pic of my junk. I just moved, so forgive the mess.
Additional reasons why my wife hates my computer obsession
Why the firewall between the two switches? Content filtering?**Update**
Why the firewall between the two switches? Content filtering?
yes, I understand that... but why? You can content filter in bridge modeit shows untangle there in bridge mode.

it doesn't make any sense unless hes using it for proxy/content filtering and or possible cacheing?
Once again, I know this is why you *might* use an untangle box for, but why have it positioned in the green side of the network. It doesn't make sense. Something like this should be moved to the perimeter of the network unless there is routing going on, which there isn't. I want to hear from the OP why he has two firewalls and not one.that's what you use an untangle box for, content/malware/spam filtering.no caching proxy as of yet, however.
I guess for the cacheing it makes sense(only because untangle doesn't support it), but other than that its just architecturally a incorrect and inefficient design. Even taking layered security into account, having two firewalls like that gains you nothing(even if you want to consider adding another layer of HA, you still have one more point of failure). Ive been doing a fair amount of architecture lately, hence the reason I want to understand why people may do stuff like this.. Its just... not rightI have an Untangle box and a pfsense box but my Untangle sits infront of my pfsense box. I like having all the content/malware/spam filtering of Untangle but I like pfsense more for routing and it does my caching.
...stuff like this.. Its just... not right. Then again, its for a house so it really dosen't matter.
hahahahcome on, you know as well as I that you should follow best practices at work AND at home!
come on, you know as well as I that you should follow best practices at work AND at home!
I guess for the cacheing it makes sense(only because untangle doesn't support it), but other than that its just architecturally a incorrect and inefficient design. Even taking layered security into account, having two firewalls like that gains you nothing(even if you want to consider adding another layer of HA, you still have one more point of failure). Ive been doing a fair amount of architecture lately, hence the reason I want to understand why people may do stuff like this.. Its just... not right. Then again, its for a house so it really dosen't matter.

Once again, I know this is why you *might* use an untangle box for, but why have it positioned in the green side of the network.
Once Untangle does caching, I'll switch over to only UT. Until then, I'll keep both though.
xphil3....I have it on the green side of my network because I don't trust Untangle at the border of my network. I prefer that a dedicated firewall be there and that the traffic filtering should be conducted on a different machine.
The traffic that isn't dropped (aka "good" traffic) by my firewall will then be further refined by my Untangle server. If the traffic manages to pass that chokepoint then it more than likely is friendly. If you think of it like a castle....I have a moat (firewall) and a drawbridge (untangle)!
Edit: It makes me sleep better at night knowing that my firewall is running software designed specifically for firewalling! Just my belief....you can put it wherever you think you should. And as far as to the interworkings of it all. The modem does the NAT'ing so it has 1 internet IP and a private range. The smoothwall does seminat routing private to private ranges with everything on the same subnet. The UnTangle sits between as a Transparent Brige...which means that it merely forwards traffic in NIC1 and out NIC2 and filters (based on apps used) all traffic flowing thru.
where else would you stick it if you only have one public IP? It sits in between your firewall and your LAN and filters all the traffic for malware and pr0n in a transparent bridge.
When people talk about cacheing, more often then not they're refering to web caching. There are multiple different kinds of web caching but they all have the same intent, to save bandwidth. What a caching server will do is store segments of website, pictures, pages that are often visited(that pass through the caching server). The problem today is that way too many sites are dynamic, causing new pages/images/p0rn to be sent through the caching server thus defeating the propose of having parts of it locally. This is a barebones description, if you want something more indepth(and it gets WAY more) look up the following:Could some one please explain caching on a network?
Could some one please explain caching on a network?
I think you're both missing the point. You're creating more potential bottlenecks and more points of failure. This is a no-no in our industry. Yes, you do gain a more layer approach to security, but once again this is nullified by the fact that you have the "one connection in, one connection out" setup. There is no redundancy, but like I said its for your home.
Phantum,
This is the explanation I was looking for, but im curious as to why you dont trust untangle at the edge of your network? You do understand that both of those UTM's do the same type of firewalling using the SAME technology(iptables), SPI. Also, many of the things that untangle can do smoothy can do. It can do antivirus/spam/url filtering so why not move those duties to the edge? That is, if you're not hardware constrained.
Yes, I understand that the untangle box does transparent filtering and I understand what that means, but keep in mind that if that box ever borks then you're transparent filtering box has no become a traffic blackhole.
Once again, you're failing to make the connection between a good design and a bunch of equipment thrown together to have some kind of enforced security blanket. Im 100% this is a no, no... trust me on this one. If you can, you always want multiple paths to exist in any kind of network to the exterior, this is how we create redundancy.Are you sure it's a no no? The way I understand it, you want only one point of entry and exit so as to minimize any route mishaps that may occur. Not to mention the fact that if someone wanted to get inside there's only one way! The redundancy I'm speaking of is in terms of security. I wouldn't go outside in a blizzard with just a t-shirt, I'd want layers! I only need a one way path to and from the internet because no matter how you slice this pie it ALL begins and ends at the modem. I've experimented with just a smoothie, with smoothie and UnTangle and just UnTangle and the differences in latency and bandwidth is negligible (+/- 2ms, +/- 10kbps).
So let me rephrase the UnTangle and edge security because it didn't come out right the first time around. It's not that I don't trust UnTangle at the edge I'd just prefer that border security (firewall) be done explicitly by a dedicated machine that doesn't do anything other than pass or drop packets! Not to mention the fact that I've got computers coming out of the demon-hole so to have two different machines doing security is actually good because then the computers aren't just gathering dust.
Im not sure if you noticed, but you totally contradicted yourself here. You say that you dont want to put all your eggs into one basket yet you want to virtualize both firewalls on one box? Then you truly have no layered security. Also, having any kind of virtual firewall to protect physical assets is a HUGE, MASSIVE no no... virtualized firewalls provide seucrity for virtual guests. This is standard.What I'd really like to do is get my ESXi server up and running so that both duties can be handled by one machine, acting as two. When it comes to security it is my belief that it's not in ones' best interests to put all your eggs in one basket. Sure both products do pretty much the same thing but the WAY in which the tasks are executed is different.
No, its not. Why do you think they created UTMs? and loadbalancing has nothing to do with this conversation, so its completely irrelevant. Ive run smoothy in your configuration, at the edge and with proxying, it all depends on the rest of your infrastructure.EDIT: I use the smoothie strictly for firewalling whereas the UnTangle is a traffic inspection (anti-virus/malware/spyware/phishing/Spam) tool. The latter could actually be done with a proxy server instead of UnTangle....which is supposed to be behind the firewall anyways (unless you're doing reverse proxying or load balancing).

No, im not wrong... I just know how to design a secure network. Read about security enclaves like I suggested to phantum and you'll understand why I suggested layered security is built in multiple paths, not one. This is the nicest way I can say to you that you need to read before you post up stuff about people being wrong. I understand defense in depth quite well, and the way that his network is designed(for a SMB or anything else) in incorrect. DiD takes into account more than just perimeter security. Modules.How is layered if each layer of security is on a seperate path? You are wrong. Layered security is like layered clothing. You HAVE to take of the pants before you can get her panties off and have full access. (otherwise the best you can get is a hand down there, i know.. but its the best analogy i could come up with)
.

I guess I can agree here, but Im taking into account both security and efficiency and correct design.Seems like each of you is speaking from a different perspective. Phantum is speaking from a security stand point which means he wants the fewest links to the outside world and as much security as he can have without it breaking the bank or degrading performance. Perfect for a company office, home network, or anything where uptime isnt the biggest concern. Uptime comes second to security.
No, im not arguing only good reliability but more a good overall network design. Again, putting two SPI firewalls(hes doing transparent, so they're both still keeping state and dropping traffic in addition to the spam/filter/et/etc) in line is NOT a layered security approach. Security must include designation of security domain, then those broken down and secured by physical firewalls, then again broken down at the access layer with proper ACL's and other security measures. He has SP edge security, that's all.... there are NO layers here. I understand the motivation of breaking out duties between devices and maybe it gives you some "quasi" layered security but again this is NOT a good design and more so a false security blanket with more negatives than positives(relating to reliability). Everything is a balance.You are speaking from a reliability stand point which means you think the most important concern is reducing the amount of weak links in the chain and having the greatest amount of links to the outside world. Better for a data center.
Security comes second to uptime.

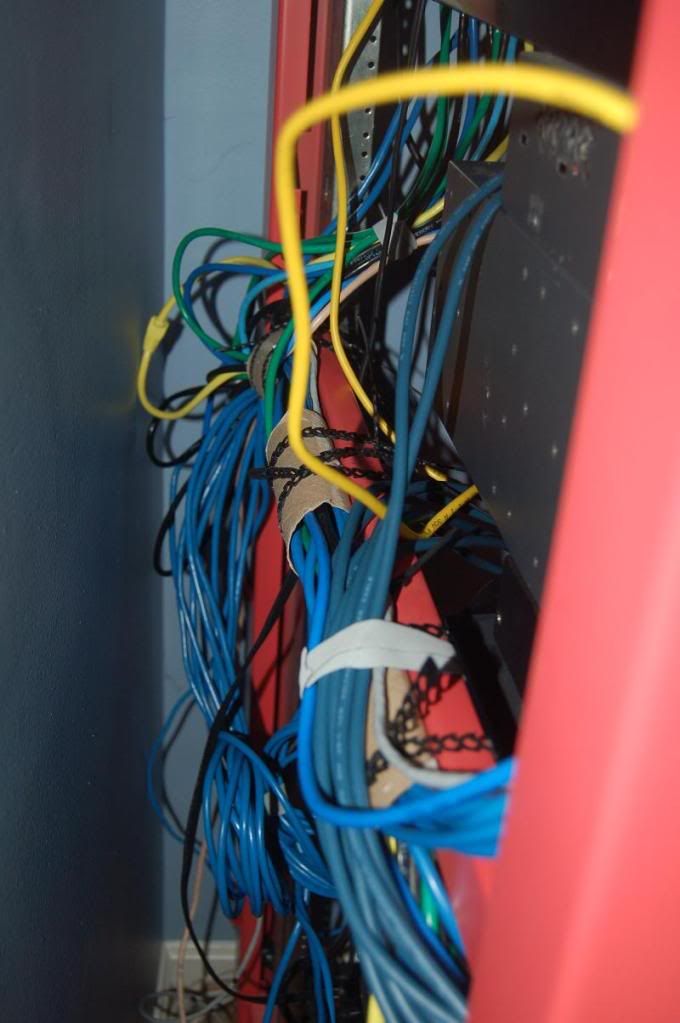

how about some toilet paper rolls!
I've used TP rolls for stuff like power strips and extension cords around the house, but hah hah for using them at work. Classic.
After taking a closer look at the last pic, it looks like you have a bunch of cables connecting the same devices. Do you have hella VLANs configured or are those connections port bonded?