Andrew_Carr
2[H]4U
- Joined
- Feb 26, 2005
- Messages
- 2,780
So somehow my home network got hacked into and I'm looking for any ideas on how to track it down and determine what to do to fix things. Last year someone also got into my email and tried resetting passwords to various sites and I got IP blacklisted from a few sites for trying logins on them too often (guessing my infected desktop that I reimaged afterwards was trying to brute-force logins to various sites I had visited such as newegg, etc.). I'm wondering if the two are linked in some way, but don't have a lot of info to go off of. I'll try to describe what happened and how my network is setup (if there's some sort of network mapping tool I could run that, just not familiar with these things).
What happened:
Earlier this week computers starting going offline and when I tried logging into my router from my phone I got a "This device is blocked" error screen. I was able to login via another computer and saw that about half of my network devices had been set to blocked by the router and knew something was wrong. I unblocked all devices and saved the router logs but more kept getting blocked and one device named "Allow" popped up (I'm guessing so they knew to block all devices except theirs). At this point I started up wireshark but then decided it'd be better to just disconnect from the internet and try to scan everything and fix the vulnerability. I did some research and disabled upnp and remote access on my router (apparently their app is required to disable that since it's not visible in the web menus). I did some virus scans on my PC and picked up nothing again, but decided to remove all the hard drives and install linux on a clean one just in case. I changed the wifi and router passwords as well just in case.
Sequence of Events:
I was able to determine that a [LAN Access from Remote] event occurred for the first time from an outside IP address about a half hour before I noticed things were going bad. There were several other IPs with the same log message that occurred shortly afterwards. There were also a bunch of SYN/ACK and RST and WinNuke scan events from various IP addresses before and during this happening but I've seen stuff like this before and it turned out to be false alarms by the router. I saved some wireshark captures but honestly I'm not sure what to even attempt to filter for.
Network setup / devices:
My Orbi router connects to my comcast modem and then to the internet. No VLANs or DMZ or anything special in-between.
Internally I have a couple orbi satellites and about 30 or so devices connected (cell phones, TVs / rokus, desktop & laptops running a mix of Windows / Mac OS, and about 27 crypto mining computers running hivelos/ubuntu linux)
No home servers or anything, the closest thing I could imagine that would draw attention is sometimes I run a full-node for crypto on my desktop when opening a wallet.
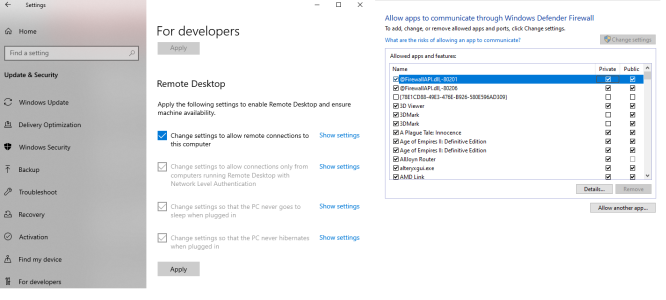
Now that I've scanned everything, changed passwords, and tried to go through my logs the only odd thing I'm seeing still is a LAN Access from Remote event from outside IPs to 192.168.1.9 on port 80. This is my desktop IP that I reimaged (I put the old windows SSD in, booted up, and then these appears in the router logs). Any other thoughts on good things to check for? I'm guessing somehow remote access is occuring on my windows device and that's how they got in? I disabled all remote access to it in windows settings awhile back when I first re-installed things, but I did install teamviewer recently to access my windows laptop remotely.
[Edit: Might've just narrowed it down. I reinstalled my windows SSD into the desktop to play a game that I couldn't get working on linux. I forgot to disconnect the ethernet cable first and now I have router logs for remote lan access that match. Guessing this is it?]
What happened:
Earlier this week computers starting going offline and when I tried logging into my router from my phone I got a "This device is blocked" error screen. I was able to login via another computer and saw that about half of my network devices had been set to blocked by the router and knew something was wrong. I unblocked all devices and saved the router logs but more kept getting blocked and one device named "Allow" popped up (I'm guessing so they knew to block all devices except theirs). At this point I started up wireshark but then decided it'd be better to just disconnect from the internet and try to scan everything and fix the vulnerability. I did some research and disabled upnp and remote access on my router (apparently their app is required to disable that since it's not visible in the web menus). I did some virus scans on my PC and picked up nothing again, but decided to remove all the hard drives and install linux on a clean one just in case. I changed the wifi and router passwords as well just in case.
Sequence of Events:
I was able to determine that a [LAN Access from Remote] event occurred for the first time from an outside IP address about a half hour before I noticed things were going bad. There were several other IPs with the same log message that occurred shortly afterwards. There were also a bunch of SYN/ACK and RST and WinNuke scan events from various IP addresses before and during this happening but I've seen stuff like this before and it turned out to be false alarms by the router. I saved some wireshark captures but honestly I'm not sure what to even attempt to filter for.
Network setup / devices:
My Orbi router connects to my comcast modem and then to the internet. No VLANs or DMZ or anything special in-between.
Internally I have a couple orbi satellites and about 30 or so devices connected (cell phones, TVs / rokus, desktop & laptops running a mix of Windows / Mac OS, and about 27 crypto mining computers running hivelos/ubuntu linux)
No home servers or anything, the closest thing I could imagine that would draw attention is sometimes I run a full-node for crypto on my desktop when opening a wallet.
Now that I've scanned everything, changed passwords, and tried to go through my logs the only odd thing I'm seeing still is a LAN Access from Remote event from outside IPs to 192.168.1.9 on port 80. This is my desktop IP that I reimaged (I put the old windows SSD in, booted up, and then these appears in the router logs). Any other thoughts on good things to check for? I'm guessing somehow remote access is occuring on my windows device and that's how they got in? I disabled all remote access to it in windows settings awhile back when I first re-installed things, but I did install teamviewer recently to access my windows laptop remotely.
[Edit: Might've just narrowed it down. I reinstalled my windows SSD into the desktop to play a game that I couldn't get working on linux. I forgot to disconnect the ethernet cable first and now I have router logs for remote lan access that match. Guessing this is it?]
Last edited:
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)