Red Falcon
[H]ard DCOTM December 2023
- Joined
- May 7, 2007
- Messages
- 12,445
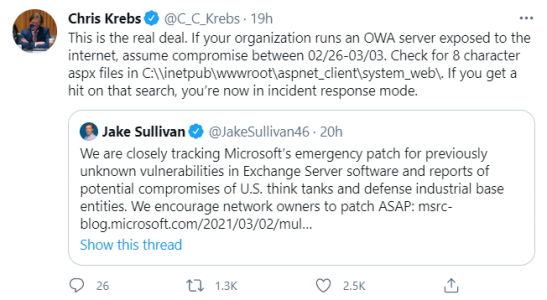
If any of you are in charge of Microsoft Exchange servers, you might want to get them patched immediately.
30,000 U.S. Organizations Newly Hacked Via Holes in Microsoft’s Email Software
30,000 U.S. Organizations Newly Hacked Via Holes in Microsoft’s Email Software
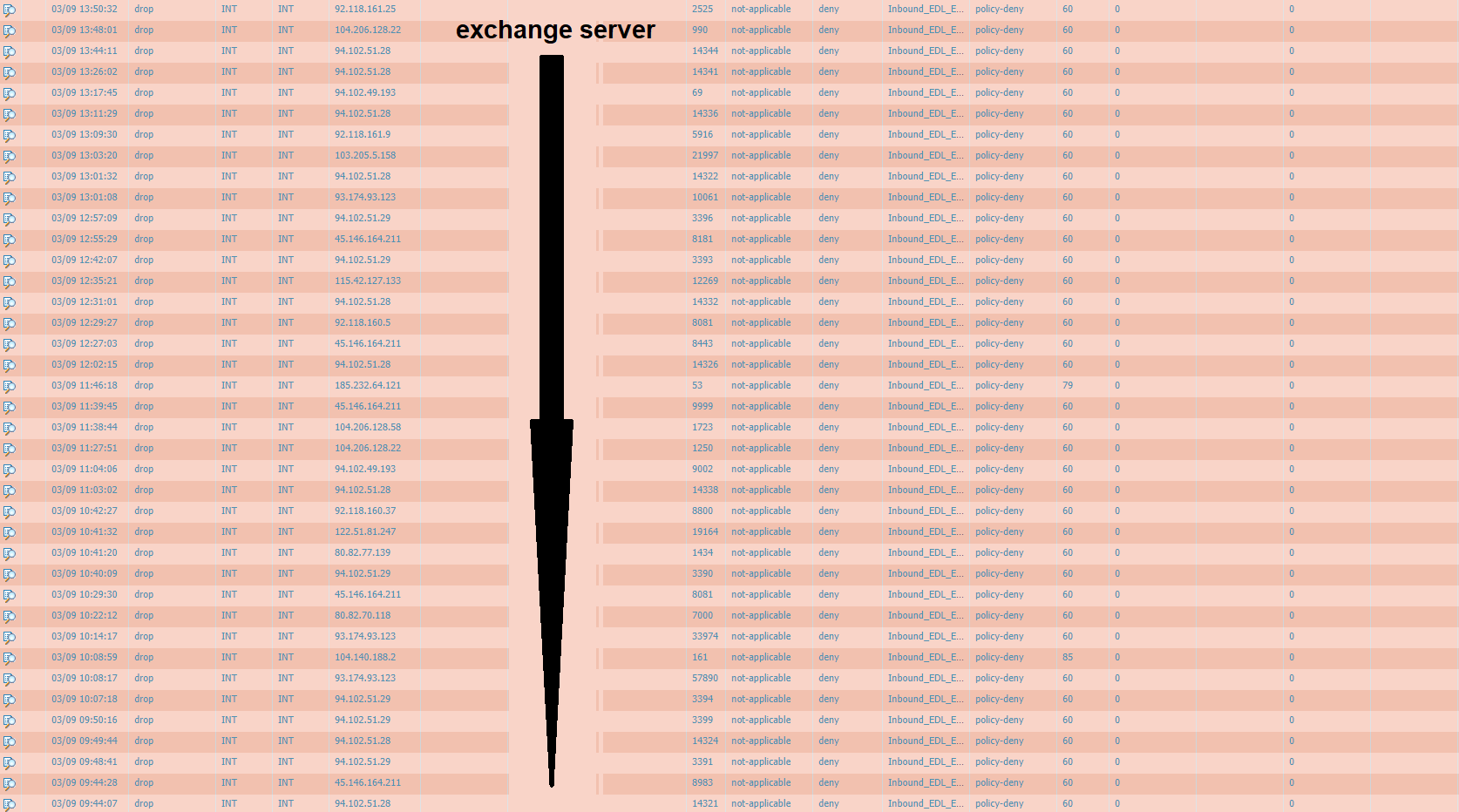
At least 30,000 organizations across the United States — including a significant number of small businesses, towns, cities and local governments — have over the past few days been hacked by an unusually aggressive Chinese cyber espionage unit that’s focused on stealing email from victim organizations, multiple sources tell KrebsOnSecurity. The espionage group is exploiting four newly-discovered flaws in Microsoft Exchange Server email software, and has seeded hundreds of thousands of victim organizations worldwide with tools that give the attackers total, remote control over affected systems.
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)